Free Tools That Make Product Notifications Easier
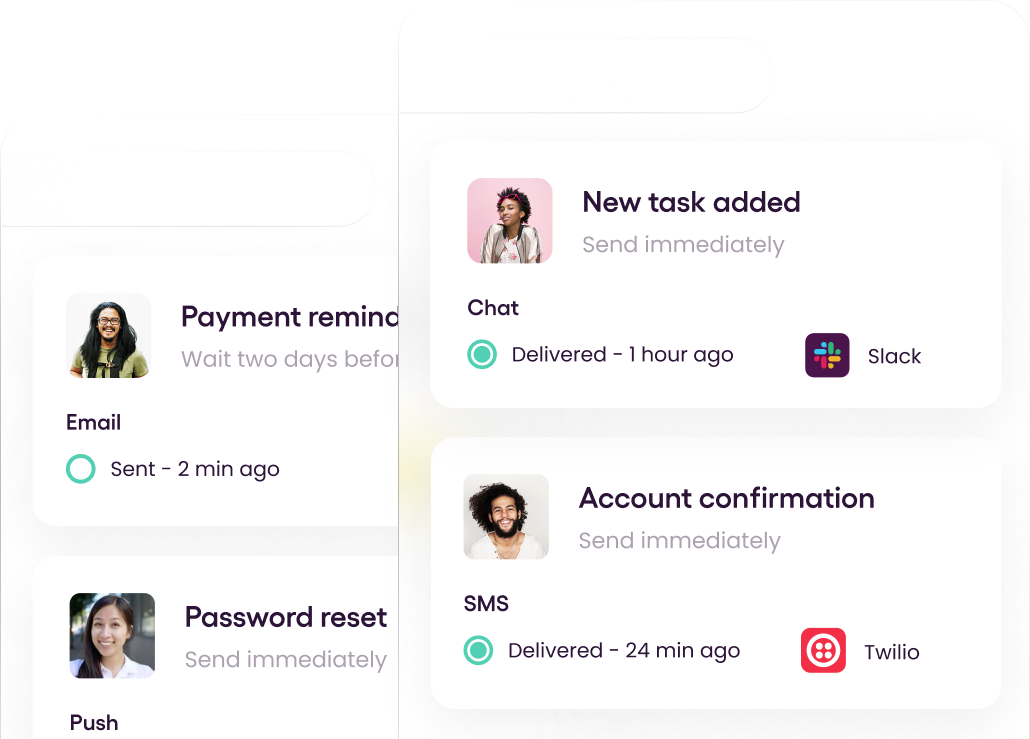
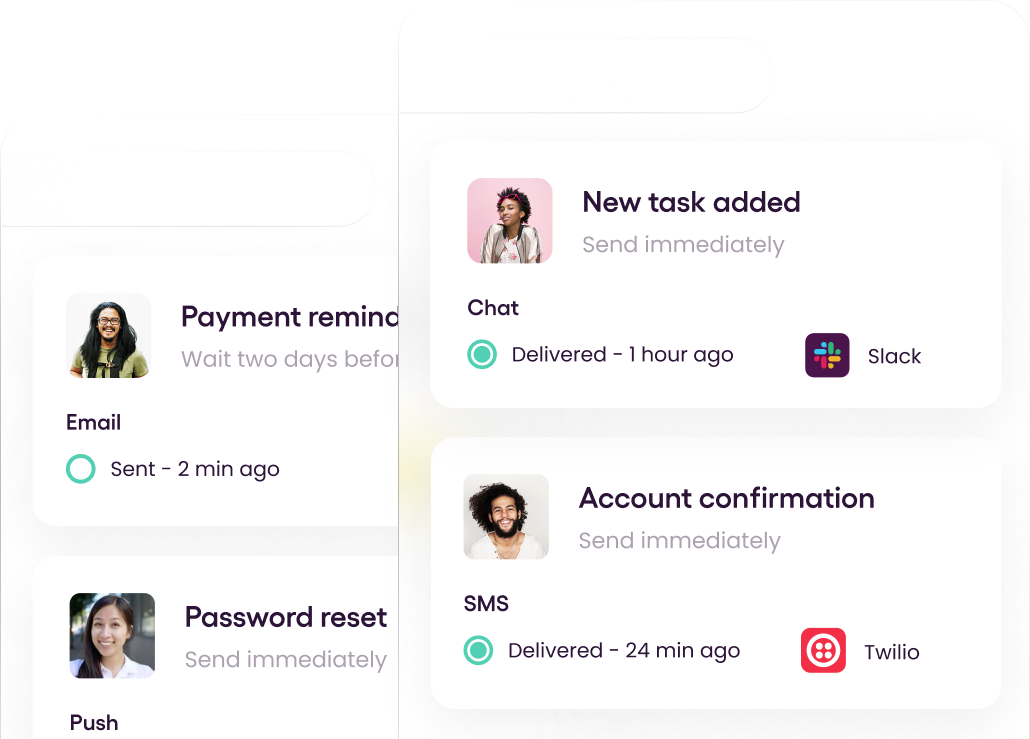
Multi-Channel
Build your first notification in minutes
Send up to 10,000 notifications every month, for free.
Get started for free
Build your first notification in minutes
Send up to 10,000 notifications every month, for free.
Get started for free
© 2024 Courier. All rights reserved.